Blog
Follow up: How do you tell if a message is a scam or not?
If you haven’t read yesterday’s blog post go and take a look at that before reading further otherwise this won’t make much sense. Shortly after publishing my article yesterday I rece... [read more]
How do you tell if a message is a scam or not?
Unless you’ve been living under a rock the chances are you have received plenty of scam messages over the last few years. Scam messages are often sent via SMS, email, WhatsApp and via social m... [read more]
Pineapples are not good for your health (yes, another cyber security post)
A Current Affair’s Martin King has just released a great five minute video about the perils of public wi-fi, do yourself a favour and watch this video. https://9now.nine.com.au/a-current-affair/... [read more]
Act now, stay secure
Christmas is a time for joy but as you spend your time with loved ones this holiday season and beyond it is important to not let your guard down when it comes to cyber security. Hackers and ransomwa... [read more]
Should you upgrade your computer to Windows 11?
Windows 11 has been available for a little over a year now but many people have been reluctant to upgrade. If you have a computer made within the last few years and running Windows 10 it is likely y... [read more]
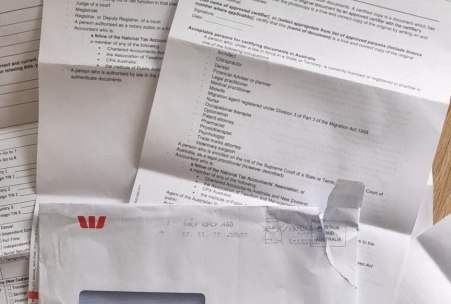
The best quality scam I have ever seen
Another day, another scam or so it seems….. Yesterday (21st November 2022) I received a letter in the post sent to my home address, it wasn’t until I opened the envelope this morning that ... [read more]
Scammers are getting more clever plus a word on 'MFA fatigue' - hear a real-life Westpac scam call.
Westpac bank has released an audio recording of a real-life scam call that demonstrates just how clever some scammers have become. Before you hit the play button below and have a listen you should fir... [read more]
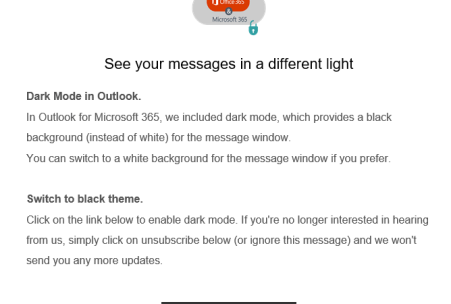
Urgent scam email alert
A new and very clever scam email is doing the rounds, it comes with the subject line “Enable Dark Mode” or similar and on the surface it appears to be a message describing the benefits of ... [read more]
Why aren't you using cloud storage yet?
Not so long ago it was common for smaller Australian business to have a slow and sometimes unreliable ADSL internet connection (remember those days?) but today there are very few businesses not connec... [read more]
Sake and USB sticks don't mix
Hot Sake in your living room might sound like a good idea at first but if you happen to have a USB stick on you with government secrets on it you should probably opt for green tea instead. I read this... [read more]
Our Services

Managed IT Support
Our fixed price Managed IT Support Programs will increase your businesses competitiveness and efficiency with our I.T. Professionals on call for you 24/7.

Same Day On-Site Support
Class leading response times ensure your that when things do go wrong we’ll be there in a hurry so you can get on with doing what your business does best.

Security and Data Protection
Custom designed security and data backup systems protect your business from emerging threats and gives you peace of mind.

Hardware and Software
We supply, install and maintain hardware and software from all major vendors including Hewlett-Packard, Microsoft, IBM, Intel and Dell all with our 30 day reconfiguration guarantee.
Testimonials

Attentive and thorough, Australia Wide I.T. get onto any of our I.T. problems quickly – with prompt, friendly and efficient service. Whenever we need to upgrade, we know we can trust their knowledge in supplying flawless new equipment that always works both physically, and to suit our needs.
Alison

Thanks for all your help today. Your patience & tenacity for solving the problem is greatly appreciated.
Jacinta

A very big thank you from me to all of the guys there….You make things so easy for us and are always available to help.
A massive shout out to the Nash though for fixing our printer – you nailed it Nash and not only changed MY life, but also helped to save some trees in the Amazon Forest!
Thanks to you all.
Jo

They’ve gotten to know our business so well and they’re truly interested in helping us. It’s like having our own I.T. Department in-house. Australia Wide I.T. takes a personal interest in our team, our business and where we’re going. They’re like family.
Other I.T. companies just didn’t seem to have the same depth of knowledge as these guys. Rather than blame the user (us) they go the extra mile, locate the problem and fix it – Every time!
Coral

My business has grown from 3 stores to 5 stores over the last 3 years; one of the unfortunate consequences of this has been the fact that our old server and network could not cope with the growth. After much deliberation we chose Australia Wide I.T. to not only arrange the supply and installation of our new network, but to also provide long term support. We have been very pleased with our decision and would happily recommend them.
Bruce

The team at AWIT deliver nothing but breathtaking service!!!!
Brett

All good as usual, keep up the professional service.
Diana

Very much appreciate your very quick response today. It was pay day today and I was a bit worried (that we wouldn’t be able to process the pays) but because of you all is well, so a big thanks.
Dale

We would recommend you to anyone, anytime.
Thank you all so very, very much for all your support. Not to mention bringing back my files to my Company. I cannot thank you guys enough.
Thanks again.
Leigh

Our previous I.T. Service Provider was distant, hard to contact and not customer focused. With Australia Wide I.T. we now have great service with a human touch. Our calls are answered promptly and the team is always ready to help in any way.
The maintenance program put in place by AWIT offers us peace of mind that our entire system is correctly and closely monitored.
Monica